Growth across regions should feel like a repeatable play, not a reinvention at every site. The fastest way to get there is by treating network stack consistency as a product your organization ships to every location. Consistency turns design principles into deployable standards. It reduces risk during acquisitions, accelerates new construction, and gives small IT teams the leverage they need to scale.
What "Network Stack Consistency" Really Means
For a technology leader, network stack consistency is the practice of standardizing the design, components, configurations, and documentation that make up your network across every site. It's helpful to think of this not as a checklist, but as a series of architectural layers.
• The Physical Foundation: This layer includes everything from structured cabling and rack layouts to labeling schemas and power standards. It's the physical "blueprint" of your site.
• The Network & Wireless Layer: This is where standards for switching, routing, VLANs, and IP schema live. It also governs the wireless experience, from site survey methodologies and SSID schemas to the authentication methods that protect your network.
• The Security & Management Plane: This layer defines your security posture, including firewall policies, network segmentation, and remote access. Crucially, it also includes the observability and control stack—your device inventory, configuration templates, and compliance checks.
A consistent stack, standardized across all three layers, produces predictable behavior. It shortens diagnostics, eliminates variance in rollout timelines, and makes every field visit more productive.
Why Multi-Regional Consistency Is So Hard
If it were easy, everyone would do it. The reality, especially for high-growth organizations, is a constant battle against variance. Each acquired site arrives with its own vendors, undocumented configurations, and shadow IT. Local constraints, from different ISPs to unique building codes, drive one-off decisions. All this is happening while a lean central IT team, often the bottleneck, tries to keep up without the benefit of standardized playbooks and templates.
MellinTech has supported multi-site groups through new builds, site conversions, and nationwide rollouts. We've seen where consistency breaks and, more importantly, how to enforce it in the field. Our two decades of experience in clinical environments like healthcare and DSOs inform the practical standards required for success.
The Business Case for Standardization
Investing in network stack consistency pays dividends against the metrics that matter most to leadership. This isn't just an IT project; it's a business accelerator.
• Accelerated Time-to-Revenue: Standard bills of materials (BOMs) and configuration templates remove guesswork, dramatically shortening the time to open a new site.
• Reduced Operational Risk: Repeatable migration plans and "golden" templates lower after-hours rework and improve cutover success rates.
• Lower Mean-Time-to-Repair (MTTR): Shared patterns and reliable documentation accelerate triage for both field technicians and central engineers.
• Improved Security Posture: Baseline policies, segmentation, and logging are enforced everywhere, not just at headquarters, reducing your attack surface.
• Predictable Capex/Opex: Procurement, staging, and field execution become forecastable, eliminating costly surprises.
Struggling to manage netword variance across your locations? MellinTech designs and executes technology programs for multi-site groups just like yours.
A Framework for Network Stack Consistency
Use this framework as both a design and operating guide. It is intentionally vendor-agnostic to fit your current and future toolsets.
1. Establish Governance and Versioned Standards
Before you design a rack, design the "operating system" for your standards. This means documenting a "Golden Site" reference architecture that includes topology, segmentation, and Wi-Fi design. Assign owners for each standard and implement a simple change-control process with version numbers. This governance model is your primary tool for deciding what won't be allowed, such as mixing unsupported hardware or running unmanaged APs.

2. Standardize the Physical Layer
The physical layer is the foundation of your entire service-level agreement. Enforcing a single standard for cabling, termination, and cabinet dressing isn't just about neatness; it's about eliminating physical-layer variance, which is notoriously difficult and expensive to troubleshoot remotely. This standard must define your labeling schema, rack and power requirements (like PDU counts and UPS runtime targets), and the mandatory closeout deliverables for every job.
(For a deeper dive, see our articles on Optimizing Network Cabling for High-Performance Dental Practices.)
3. Create a Tiered Bill of Materials
A "one-size-fits-all" standard is inefficient. A better approach is to "size" the design by site type (e.g., Tier A: Small Clinic, Tier B: Medium Facility, Tier C: Large Site). This tiered BOM approach gives procurement and field teams a clear, pre-approved shopping list. It also builds in supply chain resilience by allowing you to define functional alternates by region, so long as the management and performance profile remains consistent.
4. Publish Configuration Templates
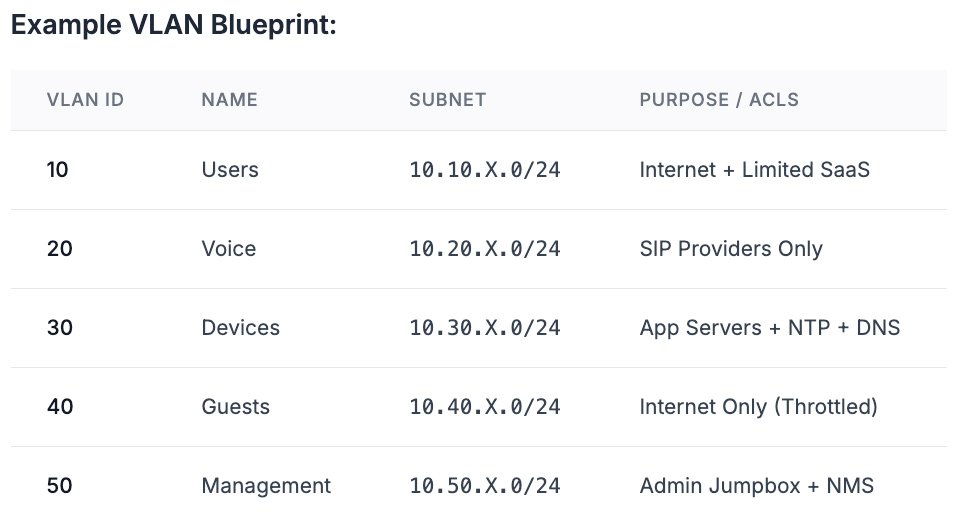
Templates are where strategy translates to repeatable execution. The goal is to templatize everything: your VLAN blueprint (with consistent IDs across all sites), DHCP scopes, SSID schema, QoS policies for real-time apps, and baseline firewall rules.
Example VLAN Blueprint:
VLAN ID
10
20
30
40
50
Name
Users
Voice
Devices
Guests
Management
Subnet
10.10.X.0/24
10.20.X.0/24
10.30.X.0/24
10.40.X.0/24
10.50.X.0/24
Purpose/ACLs
Internet + Limited SaaS
SIP Providers Only
App Servers + NTP + DNS
Internet Only (Throttled)
Admin Jumpbox + NMS
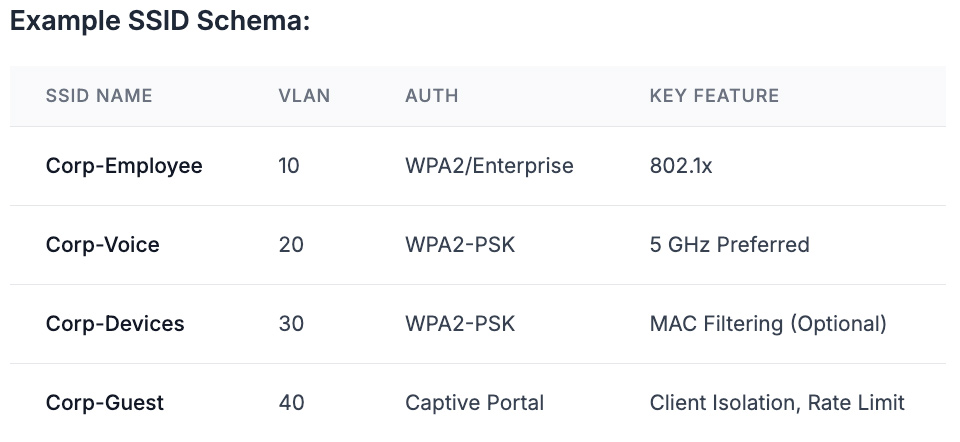
Example SSID Schema:
SSID Name
Corp-Employee
Corp-Voice
Corp-Devices
Corp-Guest
VLAN
10
20
30
40
Auth
WPA2/Enterprise
WPA2-PSK
WPA2-PSK
Captive Portal
Key Feature
802.1x
5 GHz Preferred
MAC Filtering (Optional)
Client Isolation, Rate Limit
5. Automate with Cloud-Managed Control
Leverage centralized, cloud-managed controllers to push your standard switch, AP, and firewall configurations. This is your enforcement engine. It allows you to enforce software versions, track configuration drift, and use zero-touch provisioning to dramatically reduce on-site handling and shorten cutover windows.
6. Make Documentation a Non-Negotiable Asset
Treat documentation as a balance sheet asset, not an optional task. A complete closeout package is the only way to scale your team's effectiveness. This package, containing labeled photos, cable test results, as-builts, device inventories, and final configuration exports, must be required for every job. Store these artifacts in a single, versioned repository by site code.

7. Run a Repeatable Rollout Playbook
Standardize the project phases so every rollout follows the same rhythm:
A. Discovery & Survey: ISP details, MDF/IDF conditions, power, and Wi-Fi planning.
B. Design Confirmation: Map site to Tier, validate BOM, update templates.
C. Staging: Pre-configure and label all equipment offsite.
D. Field Execution: Cabling, mounting, turn-up, and validation.
E. Cutover: Defined rollback plan and acceptance testing.
F. Closeout: Deliver documents and update the central repository.
8. Bake in Security and Compliance From Day One
Your network standard is your security baseline. Use network segmentation to isolate regulated systems (e.g., in healthcare or dental) from guest and general user traffic. Enforce least-privilege firewall rules by default, log all administrative actions, and define a process for rapidly isolating a compromised device without taking the entire site offline.
9. Prove Wireless Before You Cut Over
Wireless is the most visible part of the network; it must be flawless. Your standard must include a predictive RF design during planning, followed by an on-site validation survey. Standardize your minimum RSSI, SNR, and roaming thresholds, and maintain a test kit for critical voice and clinical applications.
The M&A Playbook in Action
This framework moves from theory to practice during acquisitions.
The Scenario:
A regional operator acquires 15 clinics across three states. The goal is to bring each site onto common standards within 45 days of closing.
The Playbook:
Week 1-2: Execute a remote discovery packet, rapid site tiering, and ISP assessment.
Week 3: Stage all hardware using "golden" templates. Ship to site, labeled by rack position.
Week 4: On-site field install, validation, and cutover during a pre-booked window.
Week 5: Closeout package delivered and central repository updated.
The Results:
Predictable cutovers, a consistent security posture from Day One, and a faster time to revenue due to a uniform onboarding process.
With over two decades in the industry, we can help build an M&A playbook for your unique situation as well.
Talk to a Technology Integration Specialist.
Common Pitfalls and How To Avoid Them
• Hardware Drift: Mixing models breaks templates. Lock a supported family per tier and review quarterly.
• Labeling Shortcuts: Skipping labels invites months of confusion. Tie project sign-off to a photo set proving all labels are in place.
• Wi-Fi Guesswork: Copying AP counts from the last project ignores construction differences. Use a predictive design and validate it.
• Undersized Infrastructure: Brownouts and heat shorten device life. Set minimums for UPS runtime and cooling, and verify them during discovery.
• "Documentation Debt": If the closeout package is optional, it won't happen. Gate project completion on its delivery.

Where Consistency Lives Across The Lifecycle
Standardization isn't a one-time project; it's a discipline.
• New Construction: Standards make "Day One Ready" predictable.
• Rollouts: Templates plus a field-tested playbook compress timelines.
• Moves, Adds, and Changes (MACs): Dispatchable services aligned to your standards keep the network clean as sites evolve.
MellinTech provides on-site MAC services and nationwide rollout management, allowing your central IT team to stay focused on strategy. We are a technology partner focused on design, build, conversions, and field execution that align to your standards.
What To Measure
You can't manage what you don't measure. Track these KPIs:
• Time from equipment receipt to site turn-up
• Number of post-cutover issues per site
• Percentage of sites at current standard version
• Mean Time to Repair (MTTR) for on-site incidents
• Percentage of projects with complete closeout packages
Quick Start: Your First 30 Days
1. Draft a one-page "Golden Site" architecture, v1.0.
2. Approve a tiered BOM with a single switch and AP family per tier.
3. Publish a v1.0 VLAN blueprint and SSID schema.
4. Choose and implement a documentation repository structure by site code.
5. Pilot the full playbook at one location and perform a structured retrospective.
Ready to Standardize Your Stack?
If you are expanding, acquiring, or upgrading across multiple regions, a consistent network stack is the fastest way to unlock speed and reliability at scale.
